Identity Suite
Where Identity Meets Intelligence
We provide a complete set of onboarding technologies — each available as a standalone module or a full end-to-end flow. Every component is compliant, fully modular, and seamlessly integrates into your product.
KYC / KYI / Proof of Identity
Document Verification
Age Verification
Liveness Check
Cross Check
Proof of Address
User Onboarding
Non-Doc Verification
Tampering Check
Document Spoofing
Document Validation
Dataspike is
In-house development allows us to respond to threats faster, be more flexible and cost-effective than competitors, while maintaining industry security and accuracy standards.
Customizable — from full stack to modules integrated within days.
Each module is independent,
accurate, and reliable.


KYC
Onboarding
We provide comprehensive coverage of client onboarding technologies: each component is available as a standalone module or as a complete end-to-end solution.
All services comply with regulatory requirements, integrate seamlessly, and can be tailored to the specific needs of your business.
Document Verification (Person)
Verification of identity documents for authenticity, structured data extraction, and field validation against country and document-specific rules
Age Verification
Determination of age eligibility through date-of-birth validation and policy-based age threshold enforcement, and AI-assisted age analysis, aligned with policy-based thresholds
Non-Doc Verification
Verification of government-issued identifiers without document images using structure, checksum validation, and trusted data source crosschecks
Document Validation
Validation of document structure, formats, checksums, and required fields according to country- and document-specific specifications (MRZ check included)
Cross Check (country/face/doc comparison)
Crosschecking of identity data across documents, biometrics, country rules, and prior sessions to detect inconsistencies and fraud
Proof of Address
Verification of residential or operational addresses through POA document validation, data extraction, and trusted source crosschecks
Spoofed/Edited Doc Detection
Detection of manipulated documents, including photoshopping, overlays, template swaps, and other tampering attempts during capture or upload
zkProof (for Web3)
Conversion of KYC results into reusable zero-knowledge proofs for privacy-preserving wallet and on-chain verification
OCR for Custom Docs
Extraction of structured data from custom document types using tailored OCR, layout analysis, and built-in tamper detection
Device Fingerprinting
Creation of persistent device profiles to identify risky environments, link sessions, and detect fraud or bot-related behavior
SSN Validation
Validation of SSNs through format, range, and checksum checks to identify invalid, recycled, or high-risk identifiers
We’re an Unified Multifunctional Platform
At its core, we are a multifunctional platform that adapts to any workflow. Each component is a clean, durable module you can assemble, customize, and analyze with precision — fully flexible, without friction.
Platform Architecture
A Platform Built For
Complete Control

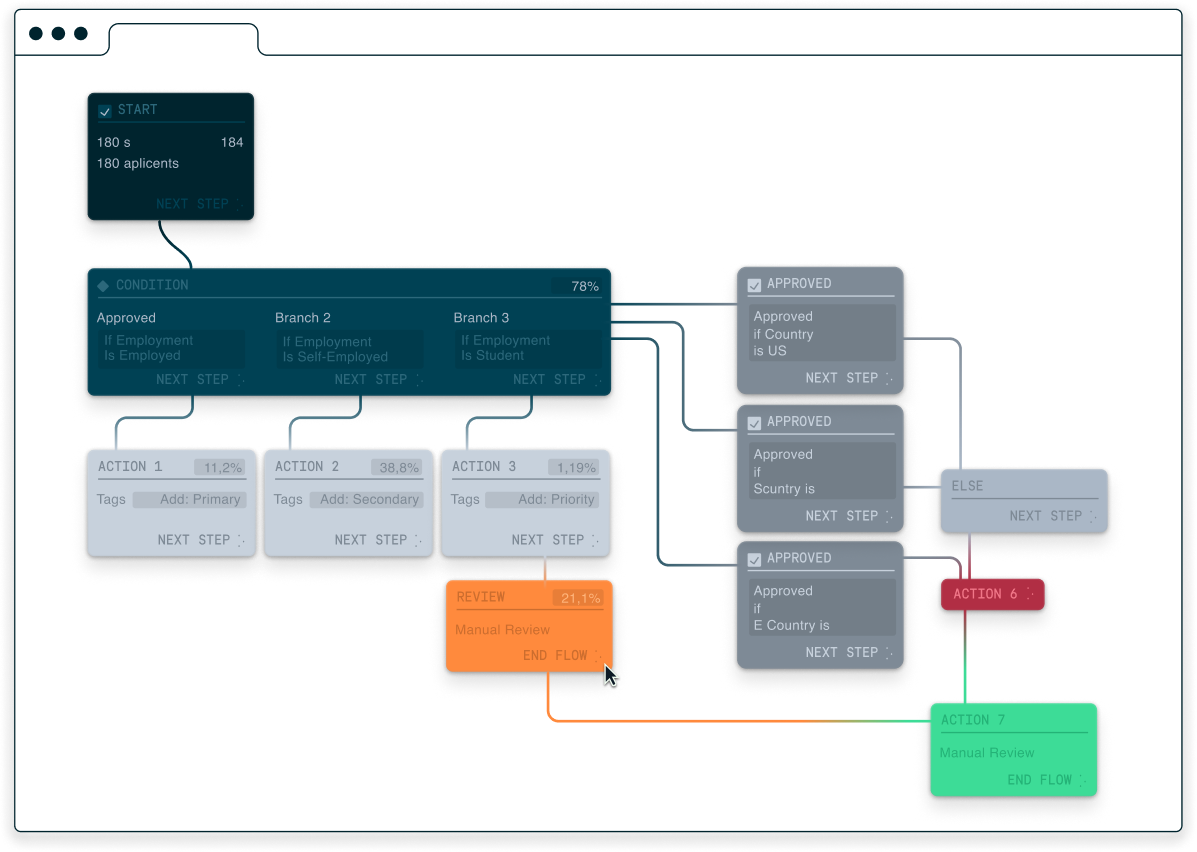
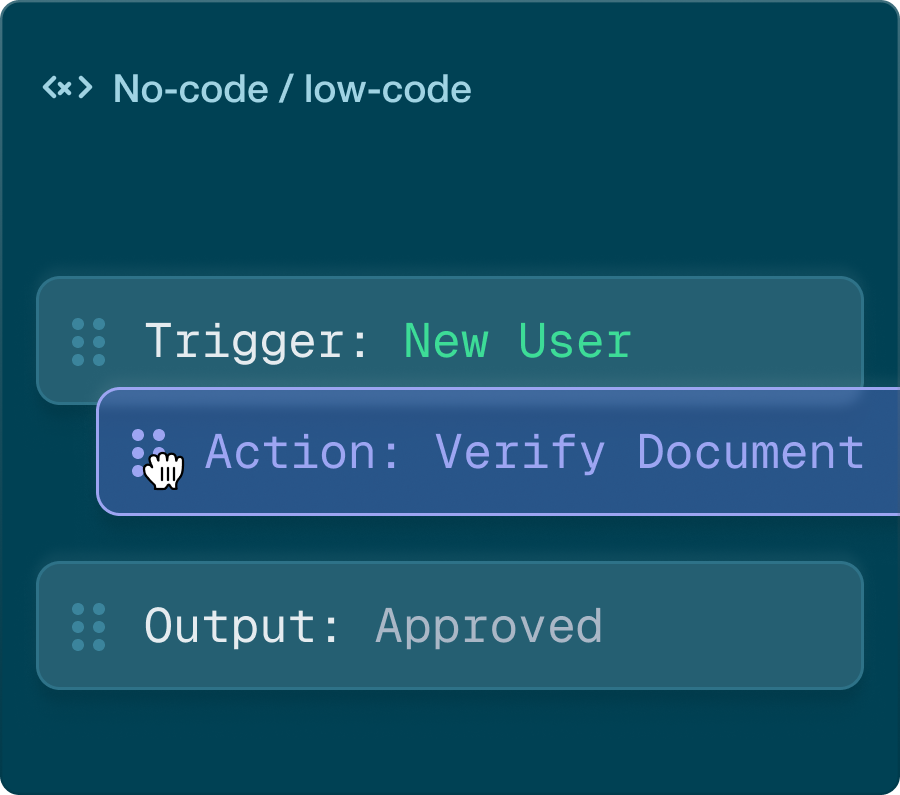
Workflow Orchestration
Configure and automate verification flows for any risk level, country, or scenario — no coding required.
- Flexible checks
- Personalized workflows
- Auto-decisions
- Risk adaptation
- Compliance readiness
- Fraud protection

Risk Scoring
Multiparameter risk assessment with adaptive scoring, behavioral signals, and real-time updates.
- Adaptive scoring
- Multifactor analysis
- Dynamic updates
- Auto score aggregation
- No-code
- Reduced manual workload
- Real-time monitoring
- Fraud protection

Customizable Analytics
Dashboards, charts, filters, and reports that give full visibility into performance and bottlenecks.
- Ready-made dashboards
- Customizable charts
- KPI monitoring
- Daily updates
- Data filtering
- CSV export
- Geographic maps
- Applicant funnel
- Risk table
- Rejection reasons
- Operational analytics
- Custom reports

Case Management
A centralized system for investigations, alerts, actions, and documents — all in one place.
- Unified investigations
- Full context visibility
- Faster decision-making
- Reduced manual work
- Checklists
- Team collaboration
- Ready-made templates
- FIU reporting
- Data traceability
- Error reduction
Customer Flow Setup
Workflow Builder
Developed in close collaboration with active compliance officers to ensure the system reflects real operational workflows: transparent risk scoring, intuitive case management, clear escalation paths, and a unified workspace for decision-making. Everything is designed to reduce operational load and increase the accuracy of controls.
Customer Flow Setup
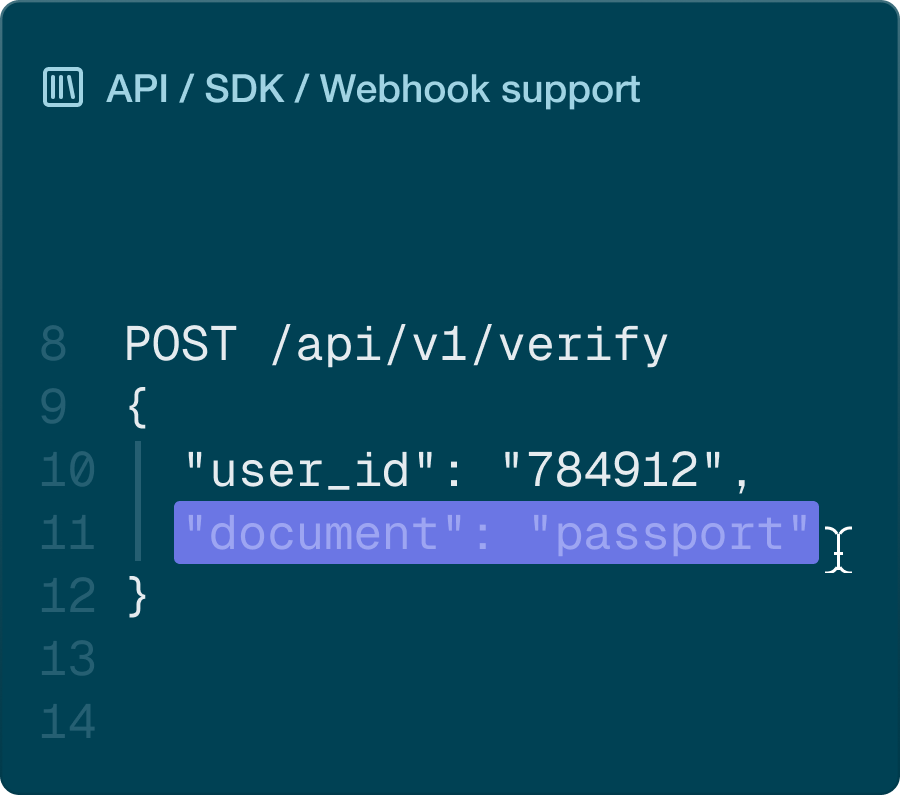
How To Deploy
Developer-friendly from the ground up: clean APIs, clear docs, real-time webhooks, and 24/7 support. Every module is plug-and-play and ready for production from day one.



other
Works seamlessly with other modules